Uncategorized
Months-Long Social Engineering Campaign Leads to $310 Million Loss at NorthRiver Exchange

April 7, 2026 — A prolonged and highly coordinated social engineering operation targeting NorthRiver Exchange has resulted in the unauthorized transfer of approximately $310 million in digital assets, according to sources familiar with the response.
The incident, which unfolded over nearly six months, is drawing attention across the cybersecurity community for its unconventional approach. Rather than exploiting software vulnerabilities or deploying malware, investigators say the attackers focused on building trust both online and in person, before leveraging that trust to gain access to legitimate systems and workflows.
Security teams have attributed the activity to a group now being tracked as Silent Ledger Collective.
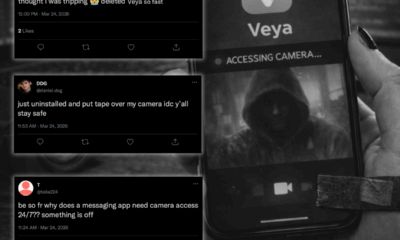
According to multiple sources, the operation began with the creation of carefully constructed digital identities. These personas were designed to appear credible within professional and cryptocurrency-focused communities, complete with consistent activity, industry engagement, and verifiable backgrounds.
Over time, the individuals behind these identities became active participants in discussions, networking spaces, and industry events, gradually establishing themselves as legitimate actors within the ecosystem.
What distinguishes this campaign from more traditional cyber incidents is its progression beyond the digital environment. Investigators say members of the group engaged in real-world interactions, meeting with professionals and stakeholders connected to NorthRiver Exchange under the guise of investors, collaborators, or strategic partners.
These interactions were described as routine at the time and did not raise immediate suspicion.
By the later stages of the operation, the group is believed to have developed trusted relationships with individuals who had proximity to NorthRiver’s operational environment. This trust, rather than any technical exploit, became the primary access vector.
Instead of breaching systems directly, the attackers appear to have gained access through legitimate channels either by influencing internal processes, obtaining authorized credentials, or operating within established workflows. Because the activity aligned with expected user behavior, it did not trigger traditional security alerts.
“The challenge here is that nothing looked inherently malicious from a systems perspective,” one source involved in the investigation said. “The actions themselves were valid. It was the intent behind them that wasn’t.”
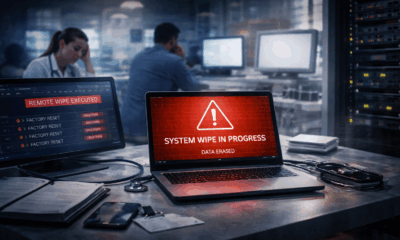
Once sufficient access was established, the group initiated a series of transactions using authenticated mechanisms. These transactions, while unauthorized in intent, were executed in a manner consistent with normal operations, allowing them to proceed without immediate detection.
By the time irregularities were identified, approximately $310 million in digital assets had already been transferred out of controlled accounts.
NorthRiver Exchange has not publicly confirmed the number of systems or accounts impacted but acknowledged that the incident involved “unauthorized activity conducted through legitimate access pathways.”
The company has since launched a comprehensive internal review, focusing on access governance, transaction authorization protocols, and third-party relationship management. Additional controls are being introduced, including enhanced verification requirements for high-value transactions and expanded behavioral monitoring to identify anomalies that fall outside of technical indicators alone.
Cybersecurity experts say the incident underscores a broader shift in the threat landscape, where attackers increasingly target human trust rather than technical weaknesses.
“This is a reminder that security isn’t just about defending systems—it’s about validating relationships,” said one industry analyst. “When an attacker can operate inside trusted boundaries, traditional defenses become far less effective.”
The blending of online persona development with in-person interaction is also raising new concerns about the convergence of physical and digital attack surfaces, particularly in industries where networking and partnership-building are core to operations.
While investigations into the full scope of the campaign remain ongoing, the incident is already being cited as a case study in how long-term social engineering can bypass even mature security environments.
There were no exploited vulnerabilities, no malware deployments, and no perimeter breaches.
Instead, the operation succeeded by embedding itself within the very systems of trust organizations rely on to function.
Watching the perimeter — and what slips past it. — Ayaan Chowdhury
Uncategorized
Trade Wars and Armed Conflicts Are Reshaping Canada’s Digital Security Strategy

Canada’s digital infrastructure is no longer just an economic asset. It is becoming a geopolitical pressure point.
As tariffs expand on advanced semiconductor components and networking hardware, and as armed conflicts reshape alliances abroad, the country’s reliance on globally sourced technology is drawing new scrutiny inside federal agencies and corporate boardrooms.
What was once a supply-chain conversation is now a security conversation.
Much of Canada’s critical infrastructure, from financial systems and telecommunications networks to healthcare platforms and cloud environments is built on hardware manufactured in politically sensitive regions and software assembled through internationally distributed supply chains. When sanctions shift or diplomatic tensions rise, those dependencies do not disappear. They tighten.
Security officials have repeatedly warned that geopolitical instability rarely stays confined to traditional battlefields. Economic retaliation now moves through cyber channels: scanning infrastructure, exploiting supply chain weaknesses, probing public services. Periods of diplomatic strain are frequently accompanied by spikes in digital reconnaissance and targeted intrusion attempts.
At the same time, modernization efforts across government and enterprise are increasing reliance on specialized AI computing hardware, much of which is concentrated among a small number of global manufacturers. Lead times are lengthening. Costs are rising. Vendor relationships are being reevaluated through a strategic lens rather than a purely commercial one.
For cybersecurity executives, the operating environment has shifted in subtle but profound ways. Risk assessments that once focused on ransomware, insider threats, and compliance exposure must now account for trade volatility, sanctions regimes, and the potential weaponization of supply chains.
The concern is not just interruption. It is leverage.
When digital infrastructure is intertwined with global politics, every procurement decision carries strategic weight. Every firmware update passes through a geopolitical filter. Every dependency becomes a potential fault line.
Canada has begun exploring diversification strategies and allied partnerships to reduce exposure. But structural realignment takes time, and adversarial cyber activity does not pause while governments negotiate trade frameworks.
For many security leaders, the conclusion is stark: digital resilience can no longer be separated from foreign policy.
In today’s climate, cybersecurity is no longer operating parallel to geopolitics.
It is operating inside it.
Covering where tech meets policy and the gaps in between. — Jordan Okeke
ODTN News’ Ayaan Chowdhury contributed to this report.
Cybersecurity
Fake QR Codes Targeting GTA Transit Riders
TORONTO, ON —
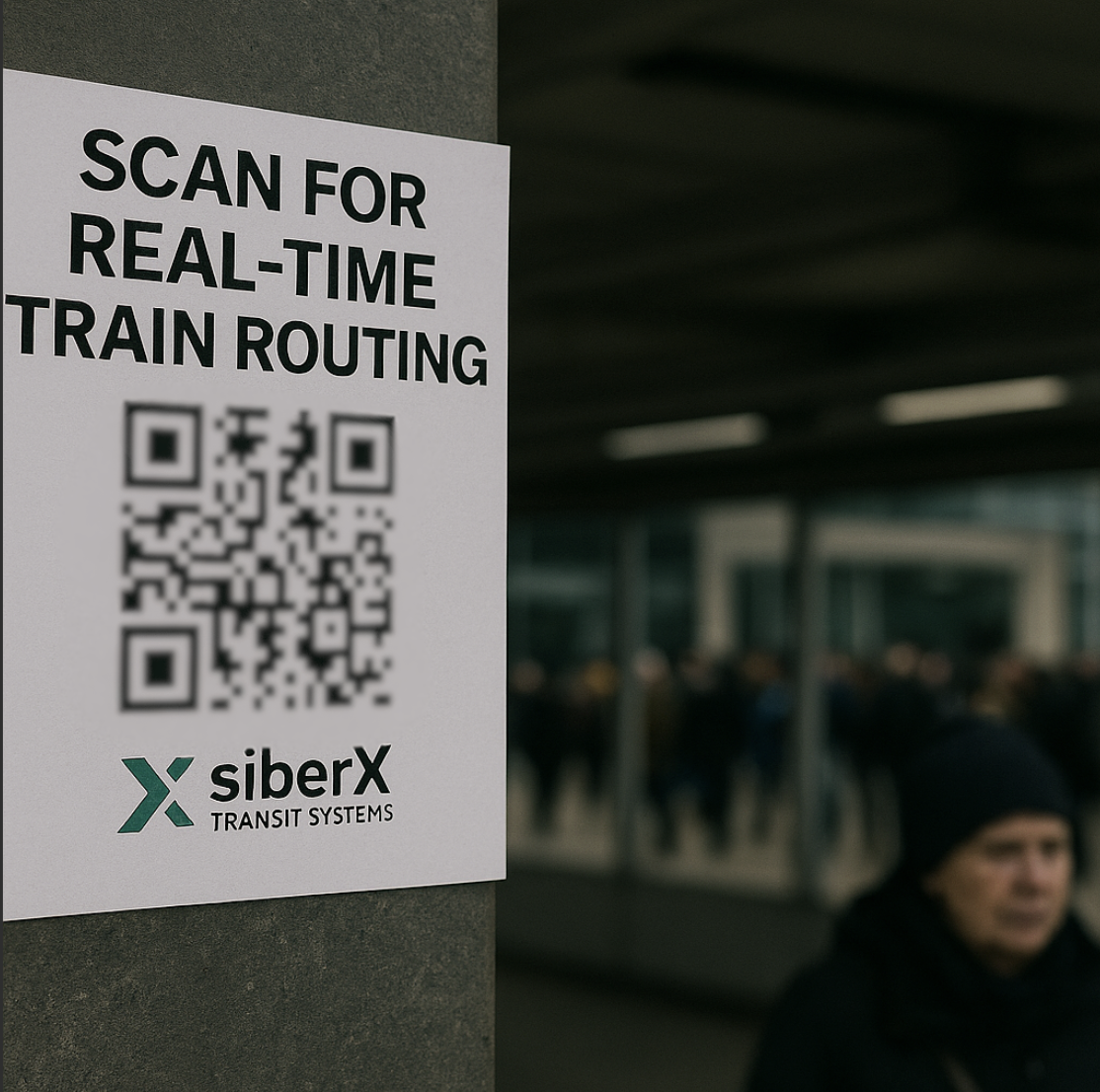
Commuters across the Greater Toronto Area are being urged not to scan a series of unauthorized QR codes that have appeared in and around multiple STS Transit stations this week. The posters, designed to look like official transit communications, promise “real-time train routing” amid ongoing service instability but cybersecurity experts say the codes actually redirect users to a malicious app that harvests personal data.
The flyers began appearing late Tuesday evening at stations in Toronto, Mississauga, Brampton, and Scarborough. Many were placed near ticket machines, station entrances, and shelters along busy commuter corridors. Their design closely mimics the colour scheme and typography of siberX Transit Systems (STS), making them nearly indistinguishable from legitimate service notices.
Security analysts consulted by ODTN say the QR codes lead to a third-party website prompting users to download an app claiming to provide “accurate route paths” during the city’s ongoing transit disruptions.
Once installed, the app immediately requests extensive device permissions — including access to contacts, location, notifications, and in some cases, stored passwords.
“This is deliberate social engineering,” said cybersecurity researcher Dr. Lena Harcourt.
“Attackers are exploiting a moment of public confusion by offering what appears to be a helpful tool. In reality, it’s a data siphon.”
Preliminary analysis shows the app transmits user information to servers registered offshore. Investigators believe the operation is linked to a broader pattern of opportunistic cyber activity that has emerged since the STS outage began.
Several commuters told ODTN they scanned the code assuming it was part of STS’s interim communication strategy.
“It looked real — same colours, same layout,” said one Brampton commuter.
“We’re all desperate for accurate info right now. That’s why people fall for this.”
Others reported seeing younger riders handing out cut flyers outside stations last night, though it remains unclear whether those individuals were aware of the scam.
STS issued a statement early Wednesday condemning the unauthorized signage and urging riders not to scan any QR codes found outside official channels.
“STS does not distribute routing information through QR posters,” the agency’s statement read.
“These materials are fraudulent and are currently under investigation.”
The incident adds another layer of complexity to a transit system already grappling with conflicting service alerts, communication failures, and worsening public mistrust.
“Criminal actors know when a city is vulnerable,” said Harcourt.
“Every gap in information becomes an opportunity for exploitation.”
Authorities are urging anyone who downloaded the suspicious app to delete it immediately, perform a device security scan, and monitor accounts for unusual activity.
What Riders Should Do
-
Do not scan any transit-related QR codes found outside official STS channels.
-
Confirm updates only through the official STS app, website, or verified social media accounts.
-
Report suspicious posters to station staff or authorities.
-
Remove any unknown app installed after scanning a QR code.
ODTN will update this story as more details become available.
Watching the perimeter — and what slips past it. — Ayaan Chowdhury
-
 Public9 months ago
Public9 months agoReddit Thread Over ‘Inventory Drift’ Surges as Canadians Vent Over Retail Glitches
-

 Business9 months ago
Business9 months agoAre Canadian Companies Learning from Global Cyber Attacks? Insider Insights into the Secret Downfall of Canadian Businesses
-

 Retail Watch8 months ago
Retail Watch8 months agoCalgary Small Business Hit by Sudden Payment Outage, Sparks Cybersecurity Concerns
-

 Cybersecurity10 months ago
Cybersecurity10 months agoCanadian Airline NorthSky Faces Cyberattack, Disrupting Online Services
-

 Business12 months ago
Business12 months agoCanadian Software Vendor Breach Exposes Cloud Environments Across Energy Sector
-

 Politics8 months ago
Politics8 months agoNationwide Government System Outage Paralyzes Public Services
-

 Retail Watch9 months ago
Retail Watch9 months agoUnderstaffed and overwhelmed, IT teams face rising pressure as retail digitization accelerates
-
 Business8 months ago
Business8 months agoInsurance Without a Safety Net? Canadian Firms Face Premium Hikes Amid Cyber Liability Crisis