Cybersecurity
Cargo Risk Algorithms Exploited to Bypass Port Inspections

Authorities and logistics security experts are investigating a suspected manipulation of cargo risk-scoring systems used to prioritize container inspections at several international port terminals, after investigators discovered patterns suggesting that high-value illicit shipments may have repeatedly bypassed screening thresholds.
According to individuals familiar with the investigation, the activity centres on a cargo targeting platform used by Northside Maritime Exchange, a global logistics coordination firm that processes shipping documentation and routing data for freight moving through major international ports. The platform aggregates information from shipping manifests, commodity classifications, declared cargo values, and historical shipment records to assist customs officials and port operators in determining which containers should receive additional inspection.
Modern container terminals process tens of thousands of shipments each day, making full physical inspection impossible. Risk-scoring systems — many of them incorporating machine learning components, help authorities identify containers most likely to require scrutiny while allowing lower-risk cargo to move efficiently through port facilities.
Investigators now believe organized smuggling networks may have discovered how to manipulate those scoring models.
Rather than attempting to breach port infrastructure or access restricted systems, the actors appear to have exploited weaknesses in the data used to evaluate shipments. By carefully altering combinations of commodity codes, shipment values, freight forwarder details, and routing information, the groups were able to repeatedly generate low-risk classifications within the targeting system. Containers associated with those shipments were consistently ranked below the threshold for additional inspection.
In several cases reviewed by analysts, cargo that would normally attract closer scrutiny including high-value electronics and restricted components was instead categorized under commodity codes typically associated with low-risk consumer goods. Investigators believe the misclassification allowed the shipments to pass through standard logistics channels without triggering deeper review. Security analysts say the technique did not involve hacking the system itself.
“The platform was operating normally,” said one logistics security specialist familiar with the case. “What appears to have happened is that the actors learned how the risk scoring weighed different pieces of shipping data, and then structured their documentation to produce the lowest possible risk rating.” Such targeting platforms are widely used across the global shipping industry. Customs authorities rely on them to prioritize inspections based on a combination of intelligence alerts, rule-based filters, and automated risk models that analyze shipment data submitted by carriers and freight brokers. While automation has dramatically improved efficiency, experts say it also creates opportunities for sophisticated actors to study and exploit the underlying logic.
“In global shipping, documentation drives everything,” said a supply chain risk analyst who has worked with international port operators. “If criminals understand which data points influence inspection decisions, things like commodity codes, shipper history, or routing paths, they can begin shaping shipments in ways that appear statistically low risk.”
The activity first drew attention after analysts reviewing historical cargo data noticed unusual patterns among shipments processed through several logistics corridors. Containers linked to the same freight intermediaries were repeatedly assigned low inspection priority despite originating from higher-risk trade routes. Investigators are now reviewing whether the activity represents a coordinated smuggling campaign or a broader vulnerability affecting automated cargo targeting systems.
Ports represent one of the most complex environments in global commerce. A single large container terminal may process more than 30,000 containers per day, with customs authorities inspecting only a fraction of that volume. Automated risk scoring systems therefore play a critical role in determining where limited inspection resources are focused. Security specialists warn that as these systems become more data-driven, they may also become more predictable.
“When algorithms are used to rank risk, patterns inevitably emerge,” the analyst said. “If someone studies those patterns long enough, they may eventually learn how to stay below the threshold.”
The case has prompted renewed discussion among supply chain security professionals about how automated targeting models should be monitored and updated to prevent manipulation. Some experts are calling for greater integration of anomaly detection tools capable of identifying unusual documentation patterns even when individual shipments appear legitimate.
For now, investigators emphasize that the incident does not appear to involve any breach of port infrastructure or customs systems. Instead, the concern lies in how shipment data itself may have been strategically structured to influence automated decision-making. The episode highlights a growing challenge as artificial intelligence and predictive analytics become more embedded in critical infrastructure. Increasingly, security experts say, the most effective attacks may not target systems directly but the data those systems rely on to make decisions.
And in global trade, where billions of dollars in goods move through automated logistics networks every day, even small shifts in how risk is calculated can determine which containers receive scrutiny… and which ones quietly pass through the world’s busiest ports.
Watching the perimeter — and what slips past it. — Ayaan Chowdhury
Cybersecurity
Advisory: Hidden Prompts in Images Raise New Concerns for AI Security

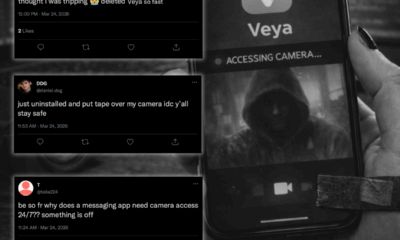
March 9, 2026 — A newly discovered artificial intelligence attack technique is raising alarms among cybersecurity researchers after demonstrating how malicious instructions can be hidden inside seemingly harmless images and later revealed to AI systems during routine image processing.
The technique, recently highlighted by security researchers studying multimodal AI models, allows attackers to embed hidden prompts within high-resolution images. While the images appear normal to human viewers, the malicious instructions become visible to AI systems after the images are automatically downscaled, a common preprocessing step used by many AI platforms.
Once the hidden instructions are revealed, the AI model may interpret them as legitimate prompts, potentially triggering unintended actions such as retrieving sensitive data, interacting with internal systems, or executing commands embedded by the attacker.
Researchers say the technique exploits a subtle weakness in how AI models process images. Many platforms reduce image resolution before analyzing them in order to improve processing speed and efficiency. In doing so, the resizing algorithm can unintentionally reveal patterns that were invisible in the original image.
In controlled demonstrations, researchers showed how attackers could embed instructions directing an AI system to extract sensitive information from documents or internal databases connected to the model’s environment.
Security specialists warn that the implications could extend beyond research environments as organizations increasingly deploy AI assistants capable of interacting with corporate systems, customer data, and internal documentation.
“If a model processes an image containing hidden instructions, it may treat those instructions as part of the user’s request,” said one AI security researcher familiar with the technique. “That creates a pathway for attackers to influence how the model behaves without the user ever seeing the prompt.”
The technique falls into a growing category of attacks known as prompt injection, where adversaries manipulate AI inputs to override safeguards or trigger unintended behaviors. While most prompt injection attacks have historically relied on text inputs, the new method demonstrates that similar manipulation can be embedded inside visual media.
For organizations experimenting with AI-driven workflows, the discovery highlights an emerging security challenge: models are increasingly expected to interpret multiple types of data simultaneously — text, images, documents, and audio expanding the potential attack surface.
Security analysts say this type of attack is particularly concerning in environments where AI tools are connected to enterprise systems, automated workflows, or internal knowledge bases.
“If the AI has access to sensitive information, an attacker doesn’t necessarily need to break into the network,” said one cybersecurity architect reviewing the research. “They only need to influence how the AI interprets the inputs it receives.”
Industry experts say the research underscores the importance of developing stronger safeguards around multimodal AI systems, including filtering mechanisms that detect hidden prompts and restrictions on how models interact with external data sources.
As AI tools continue to move from experimentation into everyday business operations, incidents like this are highlighting a broader reality for security teams: the attack surface is evolving alongside the technology.
And in some cases, the next cyberattack may not arrive as malware or phishing email but as an image that looks completely harmless.
Watching the perimeter — and what slips past it. — Ayaan Chowdhury
Cybersecurity
Luxury Resort & Casino Hit by Ransomware, Employee HR Systems Compromised

February 25, 2026 — Luxury hospitality and gaming operator Silver Court Resorts confirmed late Tuesday night that a cyber intrusion led to the compromise of sensitive employee data, following what investigators describe as a quiet, multi-stage attack that unfolded over several weeks.
The attackers are demanding 21.8 BTC (≈ $1.6M CAD) in exchange for not publishing what they claim is more than 600GB of internal HR and payroll data. While guest booking systems, casino floors, and payment platforms remain operational, internal HR infrastructure has been taken offline as forensic teams continue containment efforts.
According to sources familiar with the investigation, the breach did not begin with ransomware. It began with credentials.
Timeline of the Intrusion
January 29 – Security logs show anomalous authentication attempts against Silver Court’s legacy VPN gateway.
January 31 – Successful login from an IP address previously linked to an infostealer malware campaign. Analysts believe credentials were harvested from a finance department employee whose laptop had been infected with a commodity infostealer strain.
February 2 – Attackers deploy a legitimate Remote Monitoring & Management (RMM) tool to establish persistence. The tool blended into normal administrative traffic.
February 4–10 – Lateral movement observed toward payroll and HR file servers. Privilege escalation achieved via misconfigured service account with domain admin rights.
February 12 – Large outbound data transfer (≈ 600GB) flagged but not immediately escalated.
February 14 – Ransom note discovered on internal HR systems.
Preliminary forensic analysis indicates that the compromised data includes employee names and addresses, Social Insurance Numbers, payroll records, direct deposit banking details, benefits enrollment information, and internal HR case documentation. Security officials state that no customer payment systems were directly accessed; however, investigators caution that employee PII breaches often become stepping stones for broader fraud operations.
Threat intelligence analysts warn that exposures of this nature frequently precede identity theft campaigns, business email compromise attempts, credential stuffing against internal and customer portals, and highly targeted social engineering attacks aimed at executives and finance teams.
Incident responders believe the attack chain began months earlier when credentials were harvested through an infostealer infection. From there, an unpatched VPN appliance allowed password-based access into the corporate network. Although MFA was reportedly enabled across most systems, it was not enforced on the legacy gateway used in the intrusion. Attackers then leveraged a legitimate RMM tool to maintain access and avoid traditional malware detection. Domain misconfigurations, including a service account with domain administrator privileges, enabled rapid privilege escalation once inside.
“This wasn’t flashy,” said one responder involved in the containment effort. “It was patient. Controlled. Each step looked normal on its own. The danger was in how the pieces fit together.”
The threat group, identifying itself as “Black Meridian,” has posted a countdown timer on a Tor-based leak site, claiming it will release employee payroll data within seven days if the ransom is not paid. The organization has not confirmed whether negotiations are underway, stating only that it is working with external forensic teams and law enforcement partners.
The incident underscores a recurring reality across the hospitality and gaming sector: when revenue platforms are hardened and segmented, attackers often pivot to internal systems where monitoring thresholds are lower and data is dense. HR environments, in particular, remain one of the most concentrated repositories of high-value information inside an enterprise.
In today’s threat landscape, attackers do not always go straight for customers. They start with the people behind the business.
Watching the perimeter — and what slips past it. — Ayaan Chowdhury
Cybersecurity
New Year’s Day Cloud Disruption at Kestralyn Solutions Exposes Gaps in Automation Oversight

A service disruption at Kestralyn Solutions, a Canadian company that provides cloud-based software used by businesses to manage supply chains, inventory, and delivery operations, unfolded on New Year’s Day, a period when many staff were on holiday and routine monitoring was operating under reduced coverage.
According to information reviewed by ODTN News, the incident followed a scheduled update to an automated cloud workflow responsible for managing infrastructure scaling and system health. The change was implemented through standard processes late on December 31 and initially appeared to function as expected.
In the early hours of January 1, customers began experiencing intermittent service disruptions and delayed system responses. Internal automation processes behaved inconsistently across regions, but with limited staff on duty, the issue was not immediately recognized as a systemic failure.
Investigators later determined the disruption was not the result of unauthorized access or malicious activity. Instead, a conflict between automated scaling logic and existing resource governance policies caused infrastructure resources to cycle repeatedly. The activity was technically valid and generated no security alerts, allowing the issue to persist longer than it otherwise might have during normal operating hours.
Operations teams on call initially interpreted the issue as a temporary performance fluctuation, a common occurrence during holiday traffic shifts. Without clear indicators of a broader control-plane failure, escalation was delayed until full staffing levels resumed later in the day.
By the time engineers isolated and corrected the automation workflow, multiple customer-facing services had been affected. The company later confirmed there was no data compromise but acknowledged that reduced staffing and limited cross-team visibility contributed to the delayed response.
Industry analysts say incidents occurring during holidays and long weekends are increasingly common, as cloud environments continue to operate at full scale even when organizations do not. Automation, while essential for managing modern infrastructure, can amplify small configuration issues when human oversight is limited.
The New Year’s Day incident at Kestralyn highlights a broader operational challenge facing many organizations. As reliance on cloud automation grows, preparedness can no longer assume full staffing or ideal conditions. Systems fail on holidays, during weekends, and in the early hours often when teams are least equipped to respond quickly.
For organizations entering 2026, the lesson is not simply about improving security controls, but about ensuring resilience during the moments when attention is lowest and systems are expected to run on their own.
Watching the perimeter — and what slips past it. — Ayaan Chowdhury
-
 Public10 months ago
Public10 months agoReddit Thread Over ‘Inventory Drift’ Surges as Canadians Vent Over Retail Glitches
-

 Business9 months ago
Business9 months agoAre Canadian Companies Learning from Global Cyber Attacks? Insider Insights into the Secret Downfall of Canadian Businesses
-

 Retail Watch9 months ago
Retail Watch9 months agoCalgary Small Business Hit by Sudden Payment Outage, Sparks Cybersecurity Concerns
-

 Cybersecurity11 months ago
Cybersecurity11 months agoCanadian Airline NorthSky Faces Cyberattack, Disrupting Online Services
-

 Business1 year ago
Business1 year agoCanadian Software Vendor Breach Exposes Cloud Environments Across Energy Sector
-

 Business8 months ago
Business8 months agosiberX Mart Supply Chain Snarled as Digital Transformation Faces Cyber Threats
-

 Politics9 months ago
Politics9 months agoNationwide Government System Outage Paralyzes Public Services
-

 Retail Watch10 months ago
Retail Watch10 months agoUnderstaffed and overwhelmed, IT teams face rising pressure as retail digitization accelerates