Public
Popular Messaging App Glitch Briefly Exposes User Accounts During System Update
April 16, 2026 — A technical malfunction on the social platform Veya briefly exposed user accounts earlier today, with some individuals reporting that they were able to view messages and profile information that did not belong to them. The issue occurred during what the company described as a routine system update and appears to have affected a portion of active users before being quickly identified and contained.
In a statement issued shortly after the incident, Veya confirmed that the problem has now been resolved and emphasized that there is no evidence of a cyberattack or unauthorized external access. Instead, the company attributed the exposure to an internal system error, though it has not disclosed how many users were impacted or the full extent of the data that may have been visible.
Despite the short duration of the incident, the nature of the exposure has raised concern among cybersecurity and privacy experts. Users reported seeing fragments of private conversations and profile details associated with other accounts, pointing to a temporary breakdown in the platform’s ability to properly isolate user data — a core function of any multi-user system.
While Veya has not released detailed technical findings, early indications suggest the issue may have stemmed from how user sessions were handled during the update process. Platforms like Veya rely on session tokens to verify identity and ensure that users only access their own data. If those tokens are mismanaged — whether through improper reassignment, delayed refresh cycles, or synchronization issues during deployment — users can momentarily be granted access to information tied to another account. In parallel, caching mechanisms designed to improve performance can also introduce risk if stored data is incorrectly served to the wrong user during periods of system change.
Incidents of this nature, while not malicious, underscore the complexity of maintaining strict data boundaries at scale, particularly during live updates where systems are actively being modified. Even brief lapses can result in unintended exposure, and experts note that the impact of such events is not necessarily limited by their duration. Information that is visible, even for seconds, can be captured, recorded, or retained.
Veya is advising users to review their recent account activity and take standard security precautions, including logging out of active sessions and updating passwords. While there is no indication of ongoing risk, the incident highlights the importance of vigilance at both the user and platform level.
As platforms continue to evolve and deploy updates at increasing speed, events like this serve as a reminder that not all data exposures stem from external threats. In some cases, the risk lies within the systems themselves — in how they manage identity, access, and the invisible boundaries that keep user data separate.
For users, the expectation remains unchanged: that their information is secure and accessible only to them. For platforms, maintaining that expectation is becoming an increasingly complex challenge.
Reporting where the public speaks loudest — online and unfiltered. — Jamie Mora
Public
Viral Backlash Erupts as Messaging App Accused of Quiet Camera Access

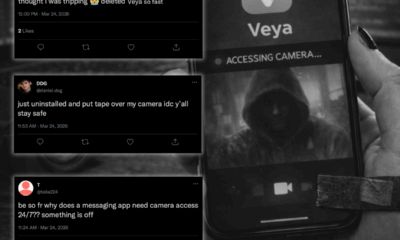
March 24, 2026 — A rapidly growing messaging platform is facing mounting public backlash after cybersecurity researchers revealed the app may have been activating users’ device cameras in the background, triggering a wave of concern and panic across social media.
The application, Veya, widely used for personal and professional communication, has come under scrutiny after analysts identified irregular camera activity tied to the app’s background processes. While the company has positioned itself as a privacy-first alternative in a crowded messaging market, recent findings suggest its use of camera permissions may extend beyond user expectations.
The issue first came to light following reports of unusual device behavior, including unexplained battery drain and intermittent camera indicator activity. A deeper technical review conducted by Northshore Digital Forensics Lab found that the app appeared to invoke camera-related functions even when not actively in use, without triggering any visible video session.
As details of the findings began circulating online, public reaction escalated quickly.
“nah bc why did my camera light blink at like 2am… i thought i was tripping 😭 deleted Veya so fast” — @mara.jpg
“be so fr why does a messaging app need camera access 24/7?? something is off” — @talia224
“we used to joke about phones watching us… yeah i’m not laughing anymore” — @laurasees
“just uninstalled and put tape over my camera idc y’all stay safe 💀” — @daniel.dog
Across platforms, users began sharing their own experiences, with some claiming they noticed brief camera activations late at night or while their devices were idle. While many of these reports remain unverified, the volume of posts has amplified concern and fueled speculation.
Cybersecurity analysts caution that while there is no confirmed evidence of images or video being recorded or transmitted, the behaviour itself raises serious questions around transparency and consent.
“This is where perception becomes reality,” said one analyst familiar with the investigation. “Even if no data is leaving the device, activating a user’s camera without clear, active intent crosses a line, especially in a consumer-facing product.”
Initial technical assessments suggest the activity may be linked to an internal feature described as a “presence intelligence” system, designed to determine whether a user is active or available. Researchers believe this module may be leveraging brief camera checks as part of its functionality, though the exact implementation remains unclear.
Veya has acknowledged awareness of the situation, stating it is “reviewing internal features to ensure they align with user expectations.” The company has not directly addressed whether background camera activation is intentional or a byproduct of the system’s design.
Meanwhile, organizations are beginning to respond. Several companies have reportedly issued internal guidance advising employees to remove the app from corporate devices pending further clarity, citing potential privacy and compliance risks.
The incident highlights a growing tension in modern app design, where advanced features powered by behavioral analytics and AI may blur the line between convenience and intrusion.
For many users, however, the technical nuance matters less than the underlying concern.
“I don’t care if it’s a ‘feature’ or not. If my camera turns on without me knowing, that’s a problem.” — @lenaaaa3
As the story continues to unfold, security experts are urging users to review app permissions, restrict unnecessary access to cameras and microphones, and remain cautious about how much trust is placed in even the most widely used platforms.
In the absence of clear answers, one thing is certain: once users begin to question whether their devices are watching them, rebuilding that trust becomes significantly harder.
Reporting where the public speaks loudest — online and unfiltered. — Jamie Mora
Public
The Hidden Risks of Having a Social Media Presence

Over the weekend, a dataset allegedly linked to approximately 8.4 million users of the popular photo-sharing app Blink began circulating in private online forums. While Blink has stated there is no evidence of a breach of its internal systems, cybersecurity observers say the information being shared. Including usernames, associated email addresses, linked phone numbers, follower counts and public profile details appears detailed enough to create real-world consequences. No passwords have been confirmed in the material. Even so, within hours of the reports surfacing, users across North America and Europe began describing suspicious password reset emails, unexpected SMS security alerts and phishing messages designed to mimic official Blink communications.
The episode may ultimately prove to be the result of automated scraping or the aggregation of publicly visible information rather than a direct intrusion. But for millions of users, that distinction offers little comfort. The incident underscores a broader reality about life online: maintaining a social media presence carries risks that extend far beyond posting photos or sharing updates with friends.
In 2026, social platforms function as more than entertainment tools. They are storefronts, professional portfolios, customer acquisition channels and, for many, primary sources of income. They also serve as digital identity hubs, linking together email addresses, phone numbers, business contacts and personal networks. When fragments of that information circulate outside their intended context, the consequences can escalate quickly.
One of the most significant risks is identity aggregation. A username on its own may seem harmless. An email address, by itself, may not appear sensitive. A phone number attached to a public profile might feel routine. But when these elements are combined, they form a verified identity footprint. Cybercriminals increasingly rely on compiling small pieces of publicly accessible or previously exposed data to build detailed personal profiles. What was once scattered information becomes a structured target list.
That aggregation fuels more convincing phishing campaigns. Security professionals warn that fraudulent messages are far more effective when they reference accurate usernames or partial phone numbers. A message that appears personalized creates urgency and credibility, increasing the likelihood that a recipient will click a malicious link or provide login credentials. Even without passwords included in a dataset, attackers can exploit trust to obtain them.
Phone numbers linked to social accounts introduce another layer of risk. SIM-swap attacks in which a fraudster convinces a mobile carrier to transfer a victim’s number to a new device can allow attackers to intercept verification codes and reset account credentials across multiple services. Once control of a primary email or social account is gained, recovery can become complicated and time-consuming.
For small business owners and creators, the implications extend beyond personal inconvenience. A compromised or impersonated account can disrupt sales, damage brand credibility and erode customer trust. Fraudsters who replicate profile names and messaging styles may target followers directly, using the credibility of an established account to facilitate scams. In such cases, the reputational impact can linger long after technical access is restored.
There is also a psychological dimension. Even when an incident does not involve confirmed internal compromise, headlines about circulating data can trigger widespread anxiety. Users may begin to question every notification or login alert. Trust in digital communication weakens. The sense of exposure, whether or not it results in direct harm can be unsettling.
Many exposures today do not stem from traditional “hacks,” but from scraping, where automated systems collect publicly visible information at scale. The misconception that public equals safe continues to persist. In reality, publicly displayed information can still be harvested, indexed and redistributed in ways that amplify risk. Once data enters underground marketplaces, it is often copied, resold and repackaged repeatedly.
Authorities have not announced any formal investigation into the Blink reports, and the platform continues to reassure users that its infrastructure remains secure. Still, cybersecurity professionals emphasize that digital visibility inevitably expands one’s attack surface. The more interconnected a person’s online identity becomes, the more valuable it can appear to bad actors.
Maintaining a social media presence is now inseparable from modern professional and personal life. But with that presence comes responsibility. Experts recommend enabling app-based multi-factor authentication, using unique passwords across platforms, minimizing publicly visible contact information and approaching unexpected security alerts with caution.
The Blink episode serves as a reminder that exposure does not always require intrusion. Sometimes it requires only accumulation, fragments of information gathered over time and assembled into something far more powerful than any single post.
In an era where identity is increasingly digital, awareness may be the most important safeguard of all.
Reporting where the public speaks loudest — online and unfiltered. — Jamie Mora
Public
Transit Chaos Ensues as Riders Report Sudden $0 Balances on siberX Transit Systems Cards

TORONTO, ON —
Morning commuters across the city were thrown into confusion today as hundreds of riders reported that their siberX Transit Systems cards suddenly displayed a $0 balance, despite many claiming they had topped up their cards within the last 24 hours.
Long lines formed at station kiosks as frustrated passengers attempted to reload their cards—only to see their funds vanish immediately. Several users said their transaction histories had been wiped clean, showing no record of recent reloads.
Transit officials have acknowledged “intermittent account visibility issues” but have not confirmed the cause. The outage comes as the city continues managing system instability from earlier disruptions.
Social media erupts
Within minutes, social platforms were flooded with posts from confused and anxious riders:
“HELLOOO?? Just loaded $50 last night and now my card says $0?? I’m not walking to work in November.” — @sarahsnotes
“Everyone at St. Andrew station is standing around tapping their cards like it’ll magically fix itself. Mine just straight up reset.” — @johnnyboy
“Why is my siberX card acting broke when I’m not???” — @throughmylens
“Can confirm: vibes terrible, balance gone, line wrapped around the platform.” — @coldbrewandchaos
Some posts also claimed that tapping a second time would “force the balance to refresh,” while others warned that “cards are being drained with every tap.” None of these claims have been verified.
Confusion spills into stations
Station staff were quickly overwhelmed as riders demanded explanations, refunds, or temporary passes. One commuter described the scene as “a mix of panic, annoyance, and people loudly Googling whether this has happened before.”
Several stations briefly halted fare-gate enforcement to prevent overcrowding, allowing riders through while the issue was investigated.
Officials urge patience
siberX Transit Systems released a short statement saying teams are “actively working to restore accurate balance information” and advising riders to avoid repeated reload attempts until the issue is resolved.
No timeline for a fix has been provided.
In the meantime, social media continues to amplify rumours, speculation, and memes—none of which are helping restore calm to an already strained transit network.
Reporting where the public speaks loudest — online and unfiltered. — Jamie Mora
-
 Public11 months ago
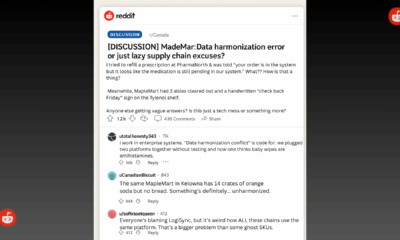
Public11 months agoReddit Thread Over ‘Inventory Drift’ Surges as Canadians Vent Over Retail Glitches
-

 Business10 months ago
Business10 months agoAre Canadian Companies Learning from Global Cyber Attacks? Insider Insights into the Secret Downfall of Canadian Businesses
-

 Retail Watch10 months ago
Retail Watch10 months agoCalgary Small Business Hit by Sudden Payment Outage, Sparks Cybersecurity Concerns
-

 Cybersecurity12 months ago
Cybersecurity12 months agoCanadian Airline NorthSky Faces Cyberattack, Disrupting Online Services
-

 Business1 year ago
Business1 year agoCanadian Software Vendor Breach Exposes Cloud Environments Across Energy Sector
-

 Business9 months ago
Business9 months agosiberX Mart Supply Chain Snarled as Digital Transformation Faces Cyber Threats
-

 Politics10 months ago
Politics10 months agoNationwide Government System Outage Paralyzes Public Services
-

 Retail Watch11 months ago
Retail Watch11 months agoUnderstaffed and overwhelmed, IT teams face rising pressure as retail digitization accelerates